

Stay Ahead of Emerging Fraud Threats
Fraud tactics continue to change as scammers use new tools and technology to target both consumers and businesses. Learn about the latest trends, what they look like, and how to protect your accounts before a scammer has the chance to act.
Reporting Local Fraud
If you suspect fraudulent activity or have concerns about your account security, please call FSB directly at (319) 377-4891.
Current Fraud Trends
Review the scams affecting people across Iowa and beyond, and see the steps that help you recognize and stop them early.

Consumer Fraud Trends
Arm yourself against fraud with expert insights on the latest Iowa trends.

Business Fraud Trend
Learn about the latest business fraud affecting Eastern Iowa organizations.

One Mistake Nearly Cost Thousands
See how a quick verification call stopped a $300,000 loss.

Counterfeit Money
Recognize the signs of counterfeit money to protect yourself.
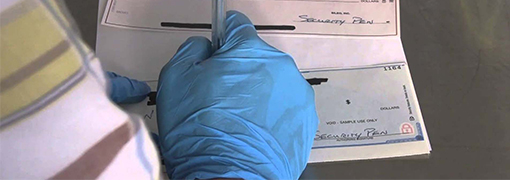
Check Washing
Discover how to prevent your checks from being altered and cashed.

Computer Security Tips
Enhance your online security to defend against digital fraudsters.

Identifying Phishing Attempts
Learn the communication tactics scammers use to trick you.

Stop Business Email Scams Early
Learn how to protect your business from email fraud.

Identifying Grandparent Scams
Learn how to spot grandparent scams and protect yourself from fraud.

Preventing Social Security Fraud
Find out how to spot and prevent Social Security fraud.


How AI Is Changing Scam Tactics
See how AI tools help scammers create convincing calls, videos, and more.

Spotting Fraud Business Calls
Learn how scammers impersonate vendors and how to verify every call.

Everyday Scams in Iowa
Learn how local Iowans spotted scams before losing money.

How Verification Prevented Loss
Learn how one business avoided a $17,000 payment scam.

Act Fast to Protect Your Money
See the steps to take right away if you sent money to a scammer.
Fraud Articles Listed
Local Fraud Trends
Money Fraud
Online Security
Targeted Scams

Stay in the Know
Get instant notifications about account activity to help you quickly catch any unauthorized transactions.

